How Does CareStack Protect Your Practice Against Cybersecurity Threats?
One of the largest dental service organizations in the United States, with over 1000 practices, recently experienced a cybersecurity attack that potentially compromised the personal information of tens of thousands of patients.
While the full extent of the data breach may unravel only in the coming days, this unfortunate incident highlights the importance of cybersecurity and urges dental practices to take proactive measures against security breaches and to protect patient data.
Patients entrust dental practices with their most sensitive information - from their medical histories to their payment details. With the increasing use of digital tools and electronic records, it's more important than ever to ensure that patient data is secure.
89% of healthcare providers suffered a cyberattack over a 12-month time frame. 2022 survey by Proofpoint and the Ponemon Institute.
Sadly, cyber-attacks and data breaches in healthcare industries are becoming more common, putting patients' personal information at risk. This can result in not only financial losses but it can also damage the trust that patients have in your practice.
Securing dental practices and patient data is a top priority for CareStack, and our comprehensive security features reflect that commitment.
Let’s take a deeper look at how CareStack prioritizes data security.
CareStack’s Cybersecurity Approach Explained
CareStack has implemented the best practices in the healthcare industry for ensuring the security of ePHI in the Cloud. We have put the following practices and measures in place to protect both CareStack and our customers against data breaches:
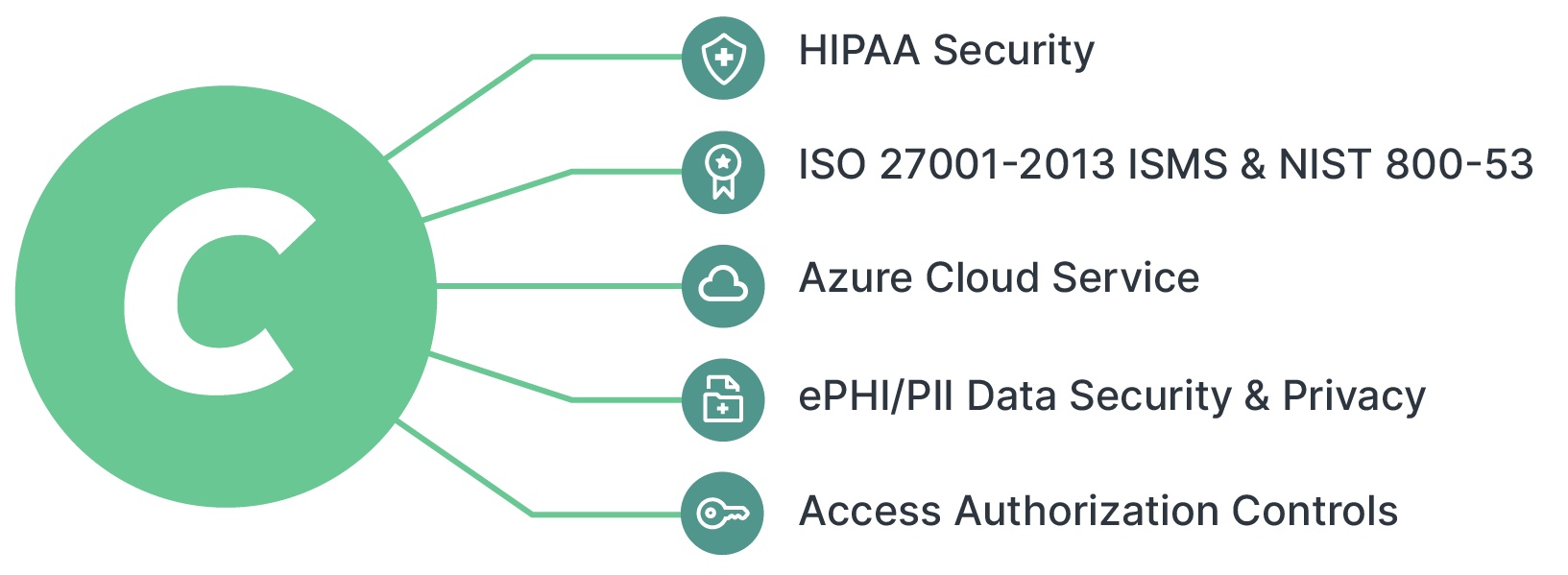
- We have implemented reasonable and suitable policies and procedures to comply with the HIPAA Security Rule's standards, implementation specifications, and other obligations.
- The required Security and Privacy Controls align with HIPAA regulations, ISO 27001-2013 Information Security Management System [ISMS] controls, and NIST 800-53 guidelines are followed.
- The CareStack architecture aligns with Azure Cloud service’s comprehensive security controls and best practices.
- To address customer concerns regarding ePHI/PII Data Security and Privacy, as well as architecture security threats, CareStack has developed and implemented a full suite of information security controls and other types of risk management.
- We have also implemented access authorization controls to the ePHI in accordance with the HIPAA security standards for the confidentiality, integrity, and availability of ePHI.
CareStack Data Security Plan

- CareStack has implemented Microsoft Azure’s Cloud security management and monitoring to aid in the management and monitoring of Azure cloud services and virtual machines.
- In order to keep the ePHI secure in the cloud, end-to-end encryption of data using AES 128-bit encrypted file systems, where each customer has an account with only the ePHI they need to accomplish their job ensuring ePHI stays intact on the CareStack environment. Unencrypted ePHI is never kept or sent.
- Encrypting data at rest and employing key management by Microsoft to keep encryption keys safe are both essential for safely storing ePHI on the cloud.
- To Increase network security and prevent network intrusion, we have implemented firewalls provided by Microsoft.
- Anti-virus software and malware detection tools are installed on all computer systems at CareStack.
- We have an agreement in place with Azure Cloud services that outlines the security controls that are implemented by Microsoft and the ability for the CareStack team to customize them.
- Role-Based Access Control: Azure role-based access control (Azure RBAC) allows authorized users to govern detailed access to Azure resources, granting only the level of access they require to do their tasks with Azure RBAC. Access is revoked when the employee leaves the organization.
- We have implemented Azure AD Multi-Factor Authentication that gives an extra degree of protection to user sign-ins and transactions. Multi-factor authentication protects data and applications while allowing users to sign in quickly. A variety of verification alternatives provided by Microsoft (phone call, text message, or mobile app notice or verification code) are also in place.
- Microsoft Azure’s Configurable security auditing and logging tools are engaged to assist in identifying security vulnerabilities. This helps us generate, collect, and analyze security logs from Azure services.
- We have a Business Associate Agreement (BAA) signed with Azure cloud services as per the requirement of HIPAA regulations.
In addition to these, we regularly implement security awareness and training programs for all our employees. Also, all CareStack employees are trained and certified in HIPAA during the onboarding process.
Conclusion
Cyber security is an essential aspect of running a modern dental practice. With the increasing digitization of patient data, the risk of cyber-attacks and data breaches has also risen. CareStack offers robust security features and measures you need to protect your patients' sensitive data in the cloud. With CareStack, you can focus on providing the highest level of care to your patients, knowing that your practice's data is safe and secure.




